Our Kickstarter campaign for our next generation of Solo products launches on January 26th. To get alerted when the campaign is live, you can sign up here.
Update: The campaign is now live! Check it out to see all the details.

Humble beginnings
I've been working on Solo for almost 3 years now. It started back when I was in college and on a whim, ordered a run of 1000 security keys that I designed and then shipped them all to Amazon.

I didn't think any would sell, but turns out they all did! Since then I've grown a team and have gone full time on this.
Thank you to everyone that has supported us and given us a chance. We are a bootstrapped hardware company and it's not easy! Your support truly helps a lot.
Solo v2
What's the difference between "Solo v1" and Solo v2? Well, just about everything!
Written in Rust. Rust is the most modern programming language for systems. Rust enables the highest level of safety and determinism which is critical for security firmware. We've completely rewritten our previous C code base in Rust, and added more functionality (like PIV). Additionally, Rust's Cargo ecosystem makes our code much more modular and suitable for open source collaboration.


Custom Provisioning. A common thought for us has been, "how can we replace JavaCard based solutions with an open source alternative?" Rust has enabled us to create a compile time based "runtime" that supports compile time defined modular, secure "apps". Our FIDO2 and PIV applications for Solo v2 are each based on this secure Rust framework. We've been building the services necessary to provision Solo v2 with custom apps, attestation keys, and other secrets. We hope to further extend this customization to enterprise. If you are using a JavaCard solution and don't like it, let us know!
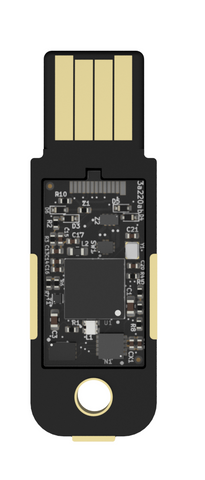
More secure microcontroller. There are a lot of secure microcontrollers out there, but very few that can be used for open source projects. Our LPC55S69 is one of the latest by NXP and doesn't require a thicket of NDAs. It supports secure boot, TrustZone, asymmetric crypto acceleration (ECC, RSA), PUF, and filesystem encryption. Together, these features enable a high level of security, secure firmware updates, speedy operations, and passive NFC operation.
More optimized NFC performance. One of the most common complaints with our v1 devices is poor NFC performance with common mobile phones. I've significantly improve the performance with v2. This is done using a more optimized and tested NFC antenna, dynamic clock scaling, a better NFC chipset, and a lower power microcontroller.
NFC honestly has been the most challenging ongoing technical problem off my life, and I've beaten it with v2. The craziest thing I had to do was set up a custom binning service for our NFC chipset, so we only take the most efficient ones.

Innovative and Robust Construction. We developed a novel construction for our new keys that is significantly more durable and waterproof. It's based on a mating of a cavity PCB and a normal PCB. After combined, the resulting electronics cavity is filled with transparent epoxy. Durability, water proof, and tamper resistant. The circuit transparency has been a big part of our open source brand, so further building on that was important to us.
The USB-C connector is welded to the cavity PCB so it is much stronger as well.


Reversible USB-A. Well this maybe wasn't the most critical feature anyone expected, but, consequence of our new PCB & case combined construction, it was easy to make USB-A reversible. So why not!


Our campaign
If you haven't yet, checkout our campaign here and preorder! Thank you so much for your support. I'm honored to be able to afford to work on this and make this a reality.